Keiter Receives Richmond-Time’s Dispatch 2026 Top Workplace Award
Read More

Why SOC Audit Quality and Credibility Matter More Than Cost
Read More
Valuation Support Through Every Stage of the Business Lifecycle
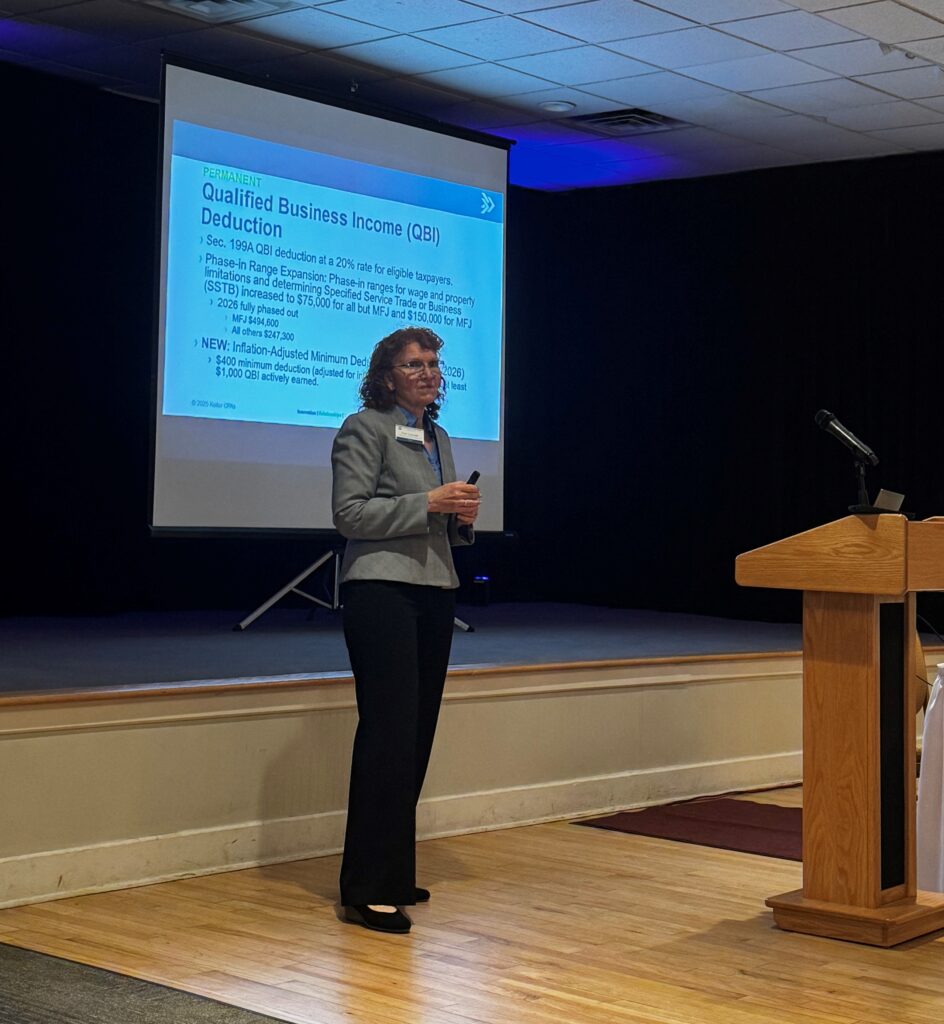
Living with the One Big Beautiful Bill Act (OBBBA)
Practical Financial Oversight for Nonprofit Boards and Volunteers
Tips for Ensuring the Schedule of Expenditures of Financial Awards is Complete and Audit Ready
ICE Reclassifies Form I-9: What Employers Need to Know
Keiter Recognized as a Brain Healthy Workplace
VFS Director Presents on Complex Business Valuation Topics at VPS Webinar
IRS Notice CP53E: What Taxpayers Need to Know About Unexpected Refund Notices
Keiter Wins Marketing B2B Award at 2026 PRSA Richmond Ceremony
What Employers Need to Know About IRS Education Benefit Updates
AI in Recruiting: What Makes Keiter’s Approach Different
What is Shaping the Construction Industry Today?